Overview
Class Central Tips
Welcome to Cryptography and Information Theory!
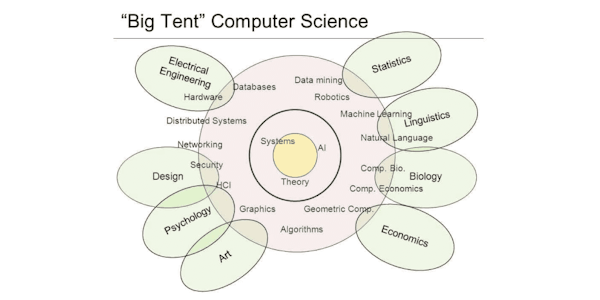
This course combines cryptography (the techniques for protecting information from unauthorized access) and information theory (the study of information coding and transfer). More specifically, the course studies cryptography from the information-theoretical perspectives and discuss the concepts such as entropy and the attacker knowledge capabilities, e.g., Kerckhoff's Principle. It also contrasts information-theoretic security and computational security to highlight the different train of thoughts that drive the cryptographic algorithmic construction and the security analyses.
This course is a part of the Applied Cryptography specialization.
Syllabus
- Cryptography Overview
- This module defines the technical terms in cryptography and introduce Alice, Bob, and Eve. To study the attacker Eve's perspective, we will describe Kerckhoff's Principle ("the attacker knows the system"), which defines the scope of the attacker knowledge (what is secret vs. what the attacker can know). We will also describe Security by Obscurity, which contrasts Kerckhoff's Principle.
- Information Entropy
- This module studies information entropy to quantify randomness. Information entropy can be used to measure the strength of the key or the secret information that determines the security of a cryptosystem against an attacker who does not know the random key.
- Brute-Force Attack and Cryptanalysis
- This module studies the attacker view whose objective is to learn the key and break the cryptographic protection using the key. First, we will define brute force attack and describe how to quantify the attacker effort for brute force attack. Next, we will contrast cryptanalysis and brute force attack. Lastly, we will discuss about perfect secrecy, which is immune to cryptanalysis and is a strong notion of security derived from information theory.
- Computational Security and Side-Channel Attack
- This module studies cryptography from the practical point of view. We will first define computational security, which relies on the fact that real world attackers are computationally limited unlike information theoretic security, e.g., one-time pad. We will then survey side channel attacks and unintentional information leakage from the physical implementations of cryptosystems.
Taught by
Sang-Yoon Chang